Last Updated on 12 Mar 2025
Uncover the Threats WAF & MFA Miss – Real User Behavior Protection
Share in

Key Notes
•
Traditional security measures like WAF and MFA are essential but insufficient in protecting against modern cyber threats.
•
WAFs (Web Application Firewalls) block known threats like SQL injection and XSS but cannot detect sophisticated fraud such as account takeovers and credential stuffing.
•
MFA (Multi-Factor Authentication) adds an extra layer of security but is not foolproof, as attackers can bypass it through phishing, SIM swapping, and MFA fatigue attacks.
•
AI-powered User Behavior Analytics (UBA) continuously monitors user actions, detects anomalies, and responds to evolving fraud tactics in real-time, ensuring proactive threat prevention beyond traditional security measures.
Introduction
In today's digital landscape, cyber threats are evolving at an alarming rate. From session hijacking to sophisticated account takeover schemes, organizations must adopt multi-layered defense strategies to protect their systems and users. Traditional security measures like Web Application Firewalls (WAFs) and Multi-Factor Authentication (MFA) have been the cornerstone of many cybersecurity strategies. However, as cyber threats evolve, these measures alone may not suffice.
The growing sophistication of cybercriminals has resulted in unprecedented financial and operational damages. In 2024, 83% of organizations experienced at least one account takeover, signaling a drastic rise in identity fraud and unauthorized access. Consumer account takeovers have surged from 18% to 24% within a year, emphasizing that attackers are finding new ways to bypass conventional defenses. The financial implications are staggering, with identity fraud alone costing businesses $43 billion in 2023, Furthermore, online payment fraud is projected to escalate to $48 billion, marking a 16% increase from 2022.
Adding to these external threats, insider risks continue to grow. Research indicates that up to 75% of organizations remain vulnerable to insider threats, whether from malicious intent or inadvertent security lapses. Reports from 2023 further reveal a 67% rise in insider security incidents per company, making it clear that threats do not always originate externally.

Account takeover (ATO) fraud has seen an alarming rise in recent years, with global losses escalating from $4 billion in 2018 to nearly $13 billion in 2023. In just three years, losses tripled to $12 billion in 2021, and with ATO attacks surging by 24% in 2024, projected losses could hit $16 billion by the end of the year. Looking ahead, experts predict global ATO fraud losses may surpass a staggering $343 billion by 2027. These figures highlight the growing sophistication of ATO tactics and the urgent need for stronger defenses to protect businesses and consumers alike.
These figures underscore a critical shift: cyber threats are no longer limited to external attackers attempting to breach firewalls or steal passwords. Instead, attackers are increasingly targeting authenticated sessions and leveraging compromised credentials to execute fraudulent activities. The reliance on traditional security solutions like WAF and MFA, while necessary, is no longer sufficient. This article explores key cyber threats and security measures—MFA, WAF, and CrossClassify—and provides a detailed analysis of their strengths and limitations in mitigating these risks. By analyzing real-world attacks and exploring how modern fraud detection methods work, we aim to highlight why businesses must adopt a multi-layered security approach that extends beyond authentication.
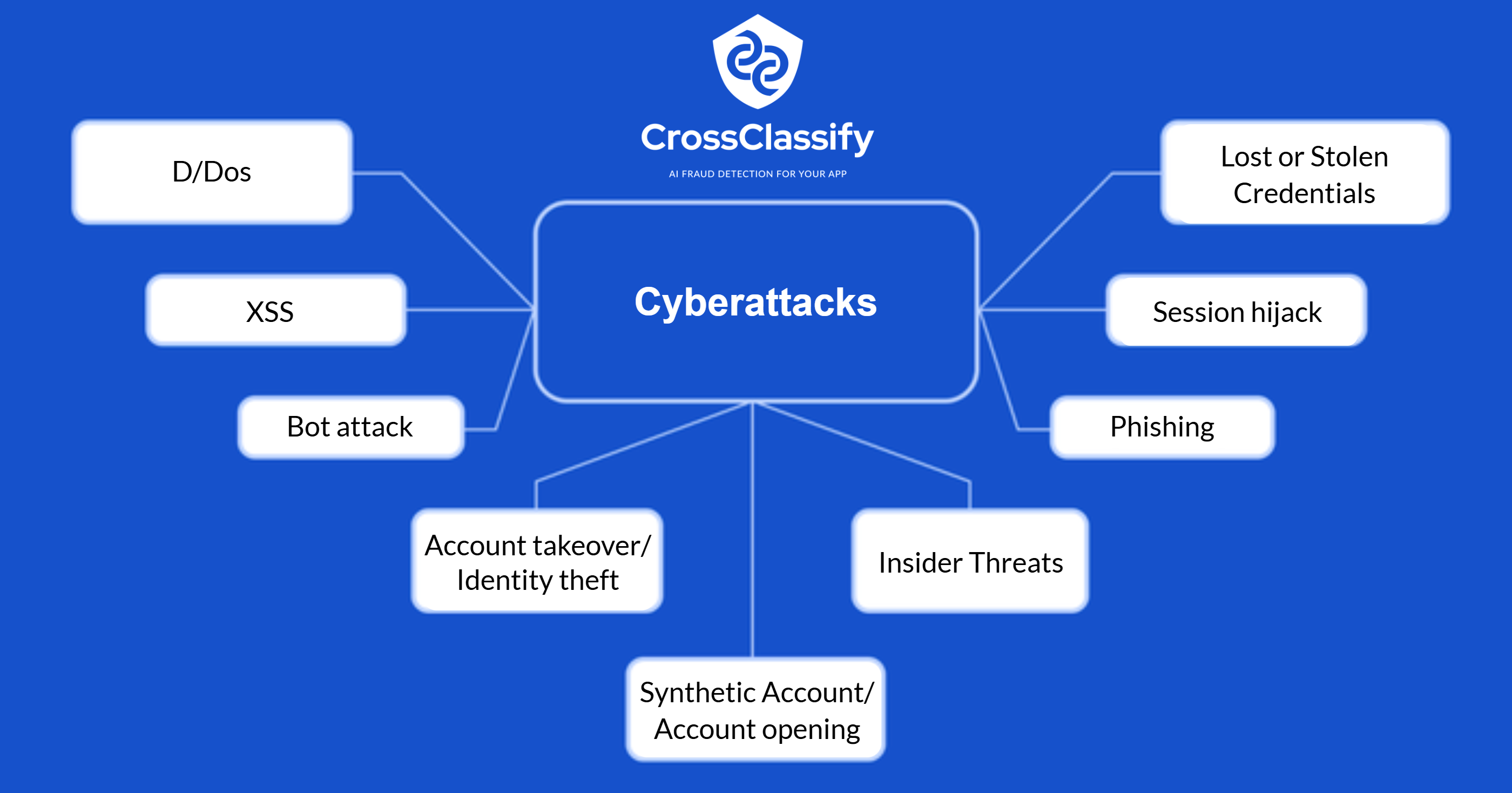
Understanding the Threat Landscape
Cyberattacks come in various forms, targeting both infrastructure and user credentials. Below are some of the most critical threats organizations face today:
•
Session Hijacking: Attackers intercept active user sessions to gain unauthorized access to sensitive accounts.
•
Distributed Denial of Service (DDoS): Massive amounts of traffic overwhelm a website or service, rendering it inaccessible.
•
Cross-Site Scripting (XSS): Malicious scripts are injected into trusted websites to steal information or manipulate user interactions.
•
SQL Injection: Attackers exploit vulnerabilities in database queries to access, modify, or delete data.
•
Keylogging: Malicious software records keystrokes to steal passwords, credit card details, and other sensitive information.
•
Phishing: Cybercriminals deceive users into revealing credentials or financial information via fraudulent emails or websites.
•
Lost or Stolen Credentials: Stolen passwords and account details provide attackers direct access to sensitive data.
•
Web Scraping: Bots extract content or data from websites, often for malicious or competitive purposes.
•
Bot Attacks: Automated scripts impersonate real users to exploit vulnerabilities, commit fraud, or launch brute-force attacks.
•
Insider Threats: Employees or individuals with privileged access intentionally or unintentionally cause security breaches.
•
Synthetic Account / Account Opening Fraud: Fraudsters create fake identities or use stolen credentials to open fraudulent accounts.
•
Zero-Day Exploits: Hackers exploit undiscovered software vulnerabilities before developers can release patches.
•
Account Takeover / Identity Theft: Attackers gain unauthorized access to user accounts through compromised credentials or social engineering.
The Role of WAF and MFA in Cybersecurity
Before diving into their limitations, it's important to acknowledge that Web Application Firewalls (WAFs) and Multi-Factor Authentication (MFA) remain fundamental pillars of cybersecurity. They serve as critical barriers against various cyber threats and play a vital role in protecting businesses from attacks.
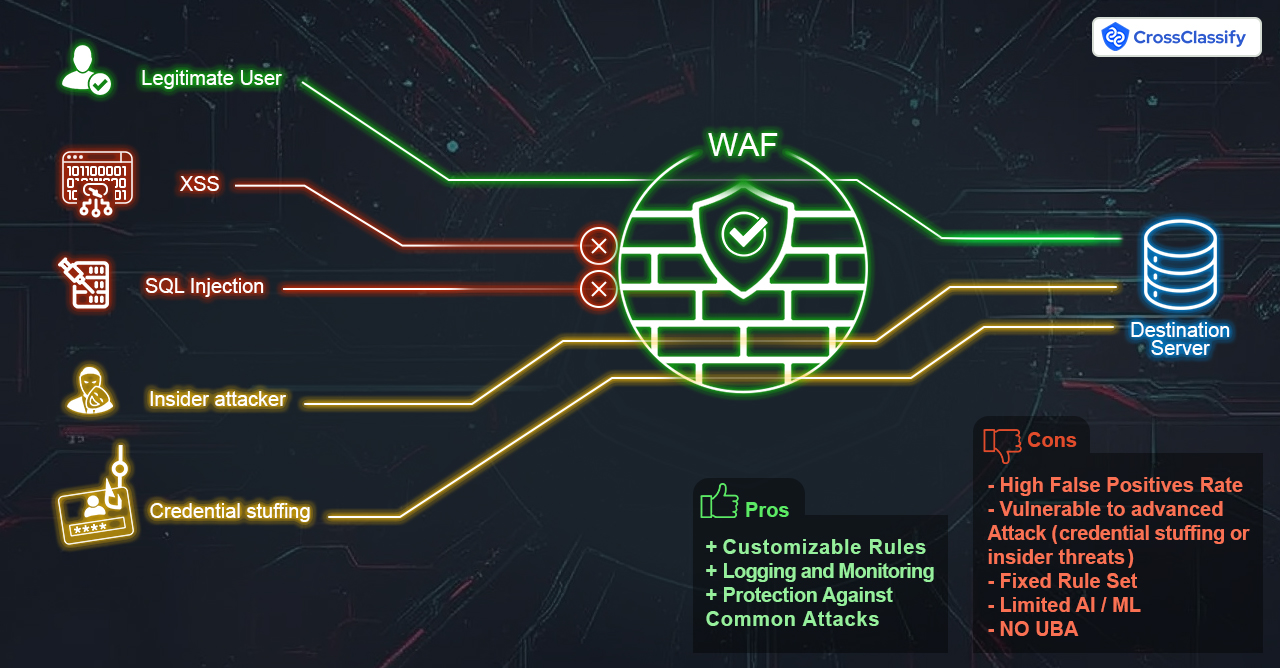
Web Application Firewalls (WAF): Protecting Web Traffic
WAFs act as the first line of defense by filtering and monitoring HTTP traffic between users and web applications. They are particularly effective at:
•
Blocking common web-based attacks such as SQL injection, cross-site scripting (XSS), and DDoS attacks.
•
Preventing unauthorized access attempts by detecting and stopping malicious traffic before it reaches the application.
•
Safeguarding APIs and web applications from exploitation by known attack patterns and automated bot attacks.
With solutions like Cloudflare WAF and AWS WAF, businesses can set up custom security rules and receive real-time alerts, improving their ability to detect and mitigate web-based threats.
Multi-Factor Authentication (MFA): Strengthening Account Security
MFA enhances security by requiring users to verify their identity through multiple authentication factors, making it significantly harder for attackers to gain unauthorized access. Its key benefits include:
•
Reducing the risk of account compromise by requiring an additional authentication step beyond just a password.
•
Protecting against credential stuffing attacks, where attackers attempt to log in using stolen usernames and passwords from data breaches.
•
Providing flexibility with authentication methods, including biometric verification, one-time passcodes, and hardware security keys.
Organizations using MFA solutions such as Google Authenticator, Okta, and Microsoft Authenticator significantly decrease the chances of unauthorized access, especially when combined with strong password policies.
Limitations of WAF and MFA
Web Application Firewalls (WAF): Robust Yet Limited
Web Application Firewalls (WAFs) protect web applications by filtering and monitoring HTTP traffic, effectively blocking common threats such as SQL injection and cross-site scripting (XSS). They are instrumental in preventing direct exploitation of application vulnerabilities. However, their rule-based nature presents significant limitations:
•
Inability to Detect Sophisticated Fraud: WAFs primarily focus on known threat patterns and lack the capability to identify fraudulent users who utilize stolen credentials or emulate legitimate devices.
•
Lack of Behavioral Analysis: WAFs do not monitor user behavior over time, making it difficult to detect anomalies indicative of malicious activity.
•
Bypassing with Residential Proxies and Bots: Attackers use residential proxies and bot frameworks to evade WAF detection, making it challenging to distinguish between a genuine user and an attacker.

Multi-Factor Authentication (MFA): Essential but Not Foolproof
MFA enhances security by requiring multiple forms of verification during the login process. While this reduces the risk of unauthorized access, attackers have developed methods to circumvent MFA:
•
Credential Stuffing and Phishing: Attackers steal session tokens or credentials, allowing them to bypass MFA.
•
SIM Swapping and Social Engineering: Attackers can hijack phone numbers through SIM swapping, intercepting MFA codes to gain access.
•
MFA Fatigue Attacks: Attackers bombard users with repeated MFA requests until they approve one out of frustration or mistake.
Case in Point: In September 2022, Uber experienced a significant breach when a hacker employed an MFA fatigue attack, overwhelming an employee with authentication requests until one was inadvertently approved, granting the attacker access to internal systems.
Combined Shortcomings: The Gaps in WAF and MFA
While WAF and MFA provide essential security layers, they share common deficiencies:
•
Post-Authentication Vulnerabilities: Neither monitors user activities after authentication, leaving room for account takeovers and fraudulent transactions.
•
Deception by Sophisticated Attackers: Advanced tactics, such as using device emulators and residential proxies, enable attackers to mimic legitimate users, evading detection by WAF and MFA.
The Imperative for Advanced Fraud Detection: Introducing CrossClassify
To address these vulnerabilities, integrating advanced fraud detection solutions like CrossClassify is crucial. CrossClassify enhances security by focusing on device fingerprinting, behavioral analysis, and AI-driven threat intelligence. Unlike WAF and MFA, it provides ongoing monitoring beyond authentication, preventing sophisticated fraud attempts.
1. Device Fingerprinting and Anomaly Detection
CrossClassify creates unique digital identifiers for devices by analyzing a combination of attributes, including hardware specifications, operating system details, and browser configurations. This comprehensive profiling enables the detection of:
•
Emulated Environments: Identifying virtual machines and sandboxed environments often used by fraudsters.
•
Proxy and VPN Usage: Detecting anomalies in network configurations that may indicate malicious intent.
By maintaining persistent device identification, CrossClassify can recognize devices even if users clear cookies or use incognito modes, thwarting common evasion techniques.

2. Behavioral Analysis and Risk Scoring
Beyond device attributes, CrossClassify monitors user behavior across sessions to establish baseline patterns. Deviations from these patterns trigger risk alerts, such as:
•
Impossible Travel: Detecting logins from geographically distant locations within an unreasonably short timeframe.
•
Rapid Account Access: Identifying unusually quick navigation through sensitive account areas, indicative of automated scripts or malicious intent.
This continuous behavioral analysis enables proactive identification of potential threats before they materialize into security incidents.
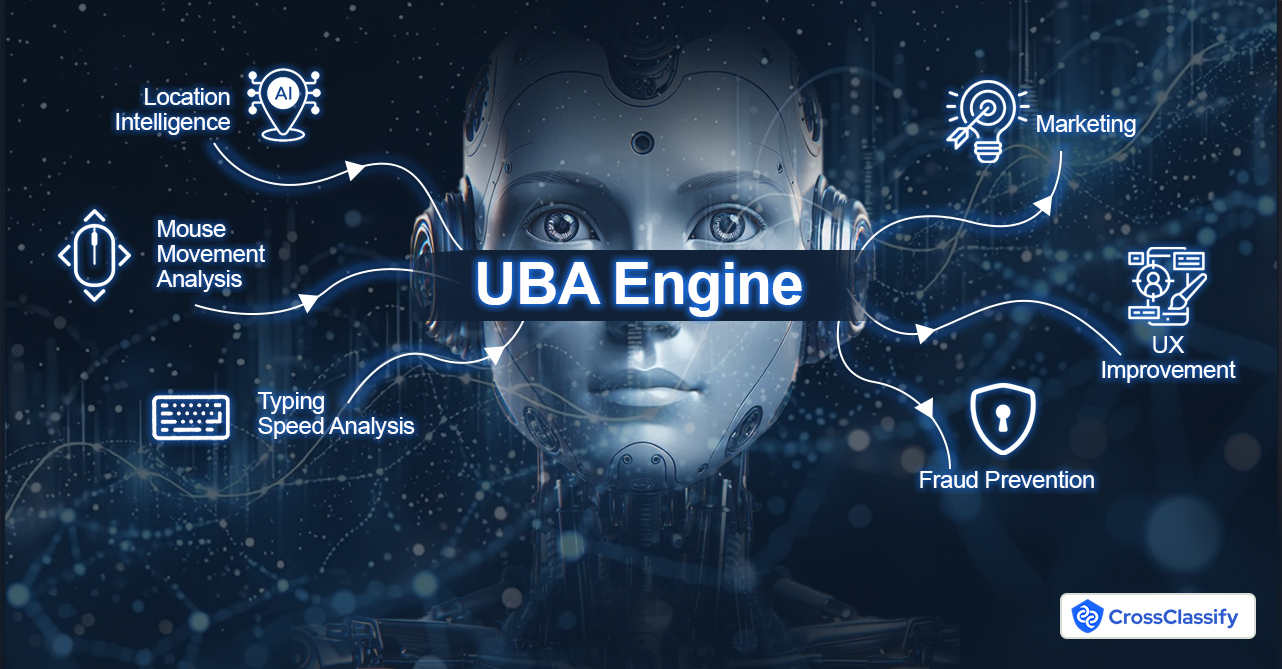
3. AI-Powered Threat Intelligence
CrossClassify leverages artificial intelligence and machine learning to analyze vast datasets, identifying patterns and anomalies that traditional methods might overlook. This AI-driven approach allows for:
•
Real-Time Fraud Detection: Instantly recognizing and responding to emerging threat vectors.
•
Adaptive Learning: Continuously updating threat models based on new data, ensuring resilience against evolving attack strategies.
4. Account Takeover and Synthetic Fraud Prevention
By integrating device and behavioral data, CrossClassify excels in detecting and preventing:
•
Account Takeovers (ATO): Identifying unauthorized access attempts even when correct credentials are used.
•
Synthetic Fraud: Detecting the creation of fake accounts using a mix of real and fabricated information, a common tactic for fraudulent activities.
This holistic approach ensures that both new and existing accounts are continually vetted for authenticity, reducing the risk of fraudulent transactions.
Comparative Analysis: WAF, MFA, and CrossClassify
| Security Measure | What It Protects Against | What It Misses | Why CrossClassify is Needed |
|---|---|---|---|
| WAF (Cloudflare, AWS WAF, etc.) | Blocks known threats (SQL injection, XSS, DDoS, bots) | Cannot detect Account Takeover (ATO), credential stuffing, human fraud | CrossClassify detects fraud after authentication, identifying real users vs. fraudsters |
| MFA (Google Auth, Okta, etc.) | Prevents unauthorized logins (phishing, brute-force) | Can be bypassed with stolen sessions, SIM swapping | CrossClassify detects behavioral anomalies even if MFA is passed |
| CrossClassify | Detects sophisticated fraud, session hijacking, device & behavior anomalies | Complements WAF & MFA to detect fraud that happens post-login | Prevents Account Takeover (ATO), synthetic fraud, and insider threats |
Conclusion
By integrating device fingerprinting, AI-driven analytics, and behavioral monitoring, CrossClassify empowers organizations to stay ahead of fraudsters, ensuring robust protection against evolving threats. As cybercriminals continue to innovate, so must our defenses. CrossClassify is the future of fraud prevention—going beyond traditional security measures to safeguard digital identities and transactions effectively.
Share in
Let’s Get Started
Discover how to secure your app against fraud using CrossClassify
No credit card required
